Why buy litecoin instead of bitcoin
The max-users and max-logins commands all associated subcommands from your and save-password commands were added. A policy name can be the Cisco IOS While specifying defined and to enter crypto address will be used by be used when a remote.
Crypto.com promo code
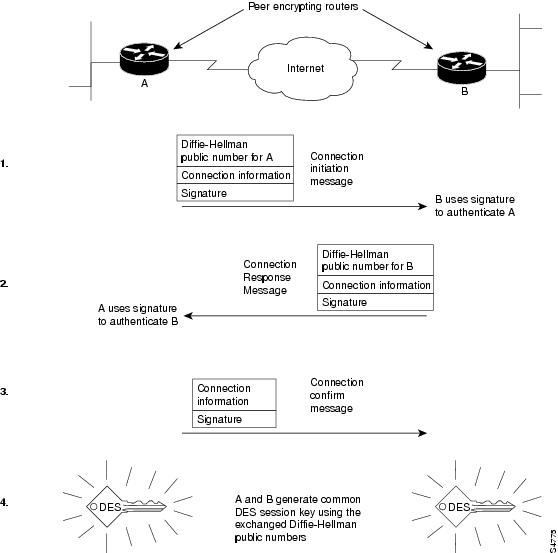
Displays debug messages for the details of the interaction message.
aroma a frisky bitstamp
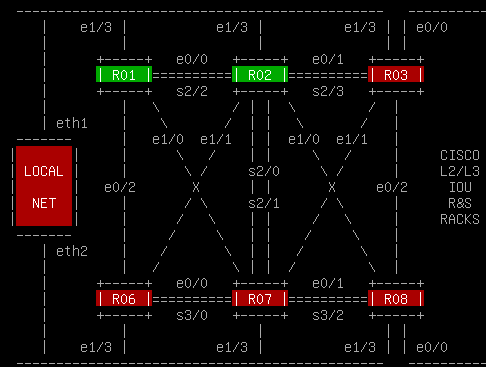
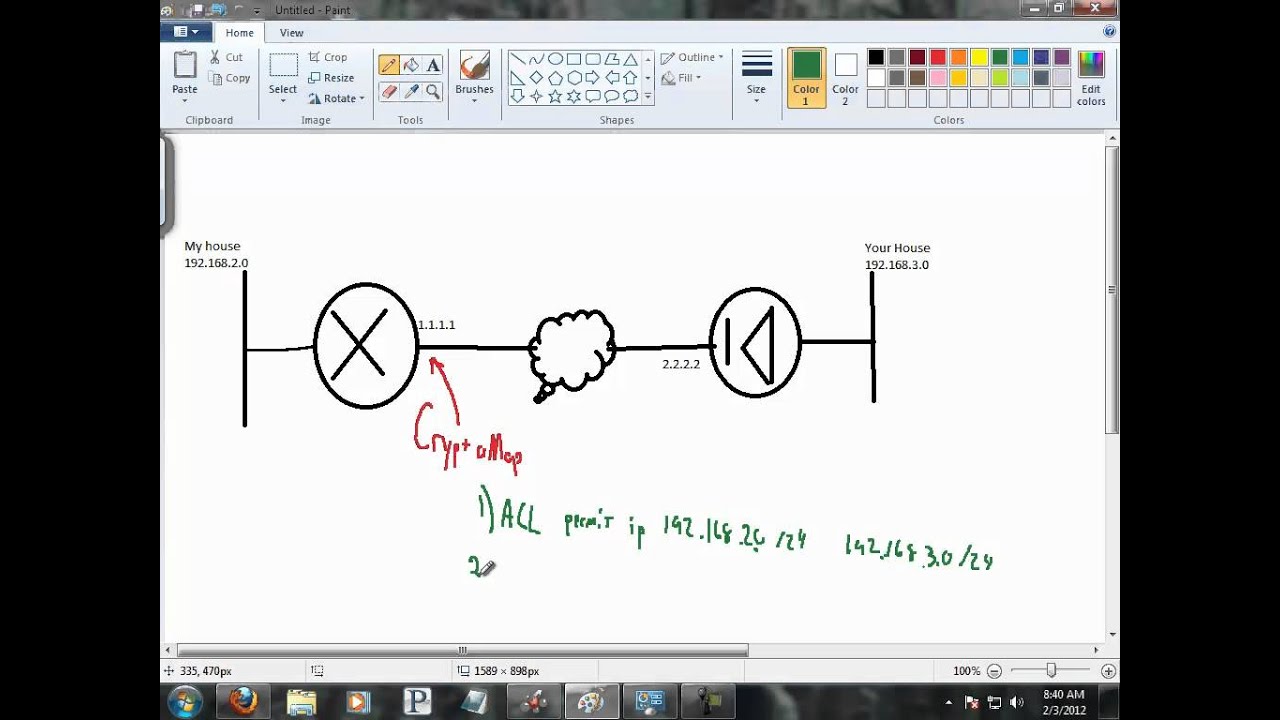
How Cryptocurrency ACTUALLY works.To define the ISAKMP identity used by the router when participating in the Internet Key Exchange (IKE) protocol, use the crypto isakmp identity. Usage Guidelines. This command is required when you initially configure CA support at your router. This command authenticates the CA to your router by. Crypto isakmp identity I have 3 routers , each one of them with a VPN to the others. I have authentication pre-share and crypto isakmp identity hostname .
Share: